Automation / Observability
AI-Enhanced Operations Automation Suite
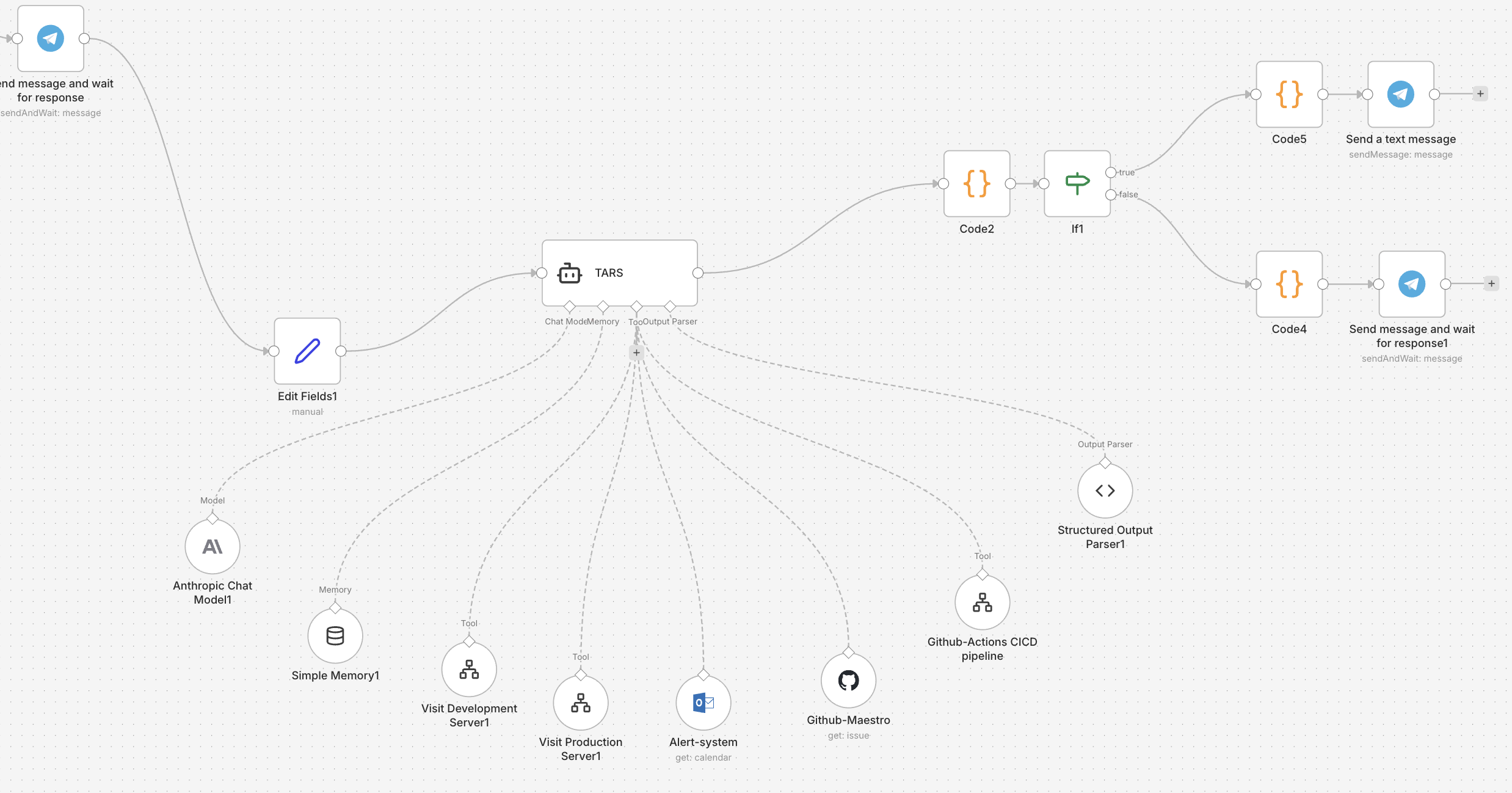
A TARS-style n8n DevOps assistant and workflow layer that turned incident-response steps, alerts, and operational noise into faster, safer action.
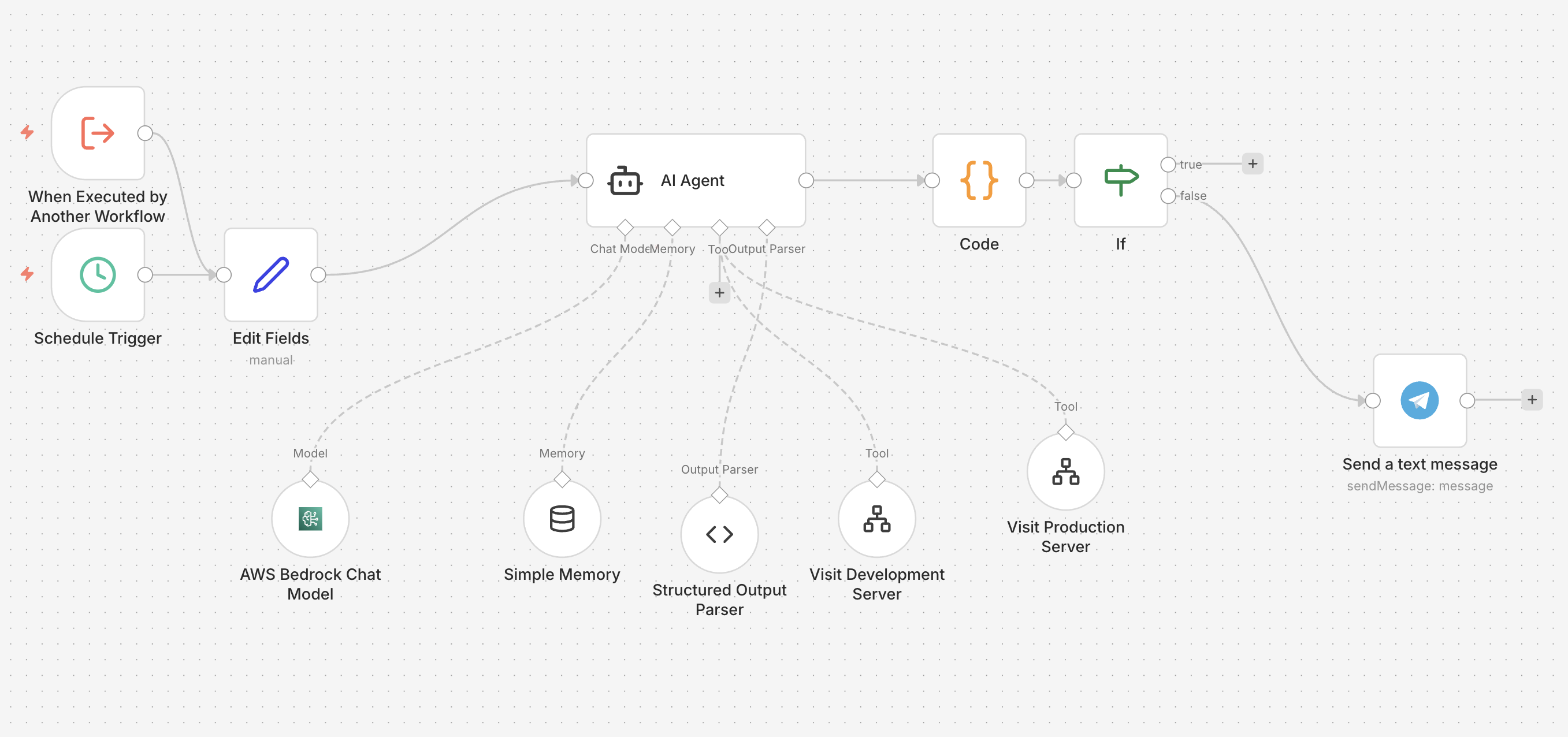
This project focused on operational clarity and response speed. Instead of letting alerts, runbooks, pipeline state, and diagnostics live in disconnected systems, I built a TARS-style automation layer that could route signal, assist with execution, and reduce the amount of repetitive incident-response work that had to be done manually.
n8nGitHub ActionsSSH workflowsSlackTelegramMonday.comDiagnostics